UNDERSTAND YOUR M365 SECURITY RISK AND PRIORITIES
Microsoft 365 Security Assessment
Delivered by the Sourcepass Center of Excellence for Microsoft
Identify and Prioritize your M365 Risk
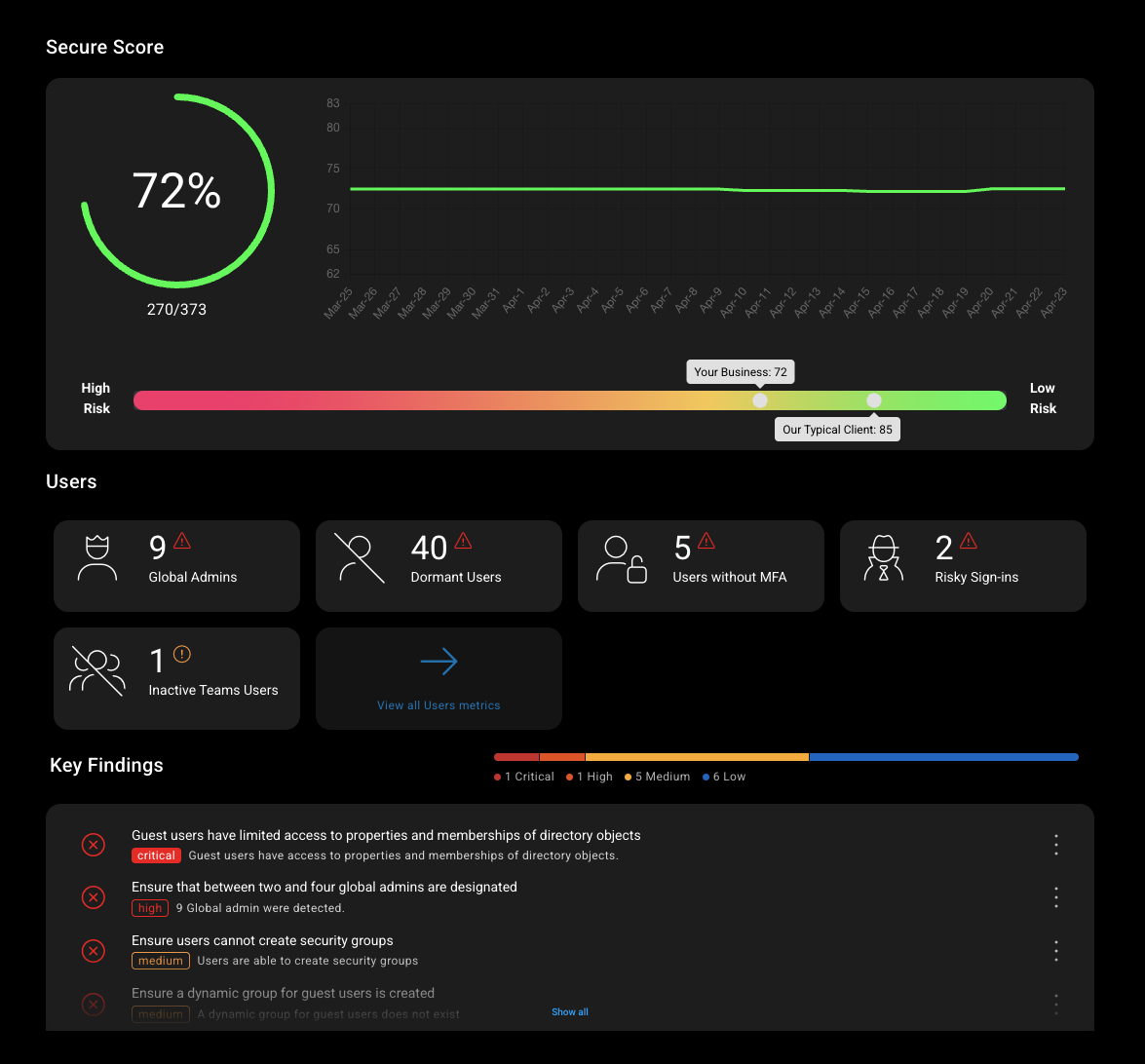
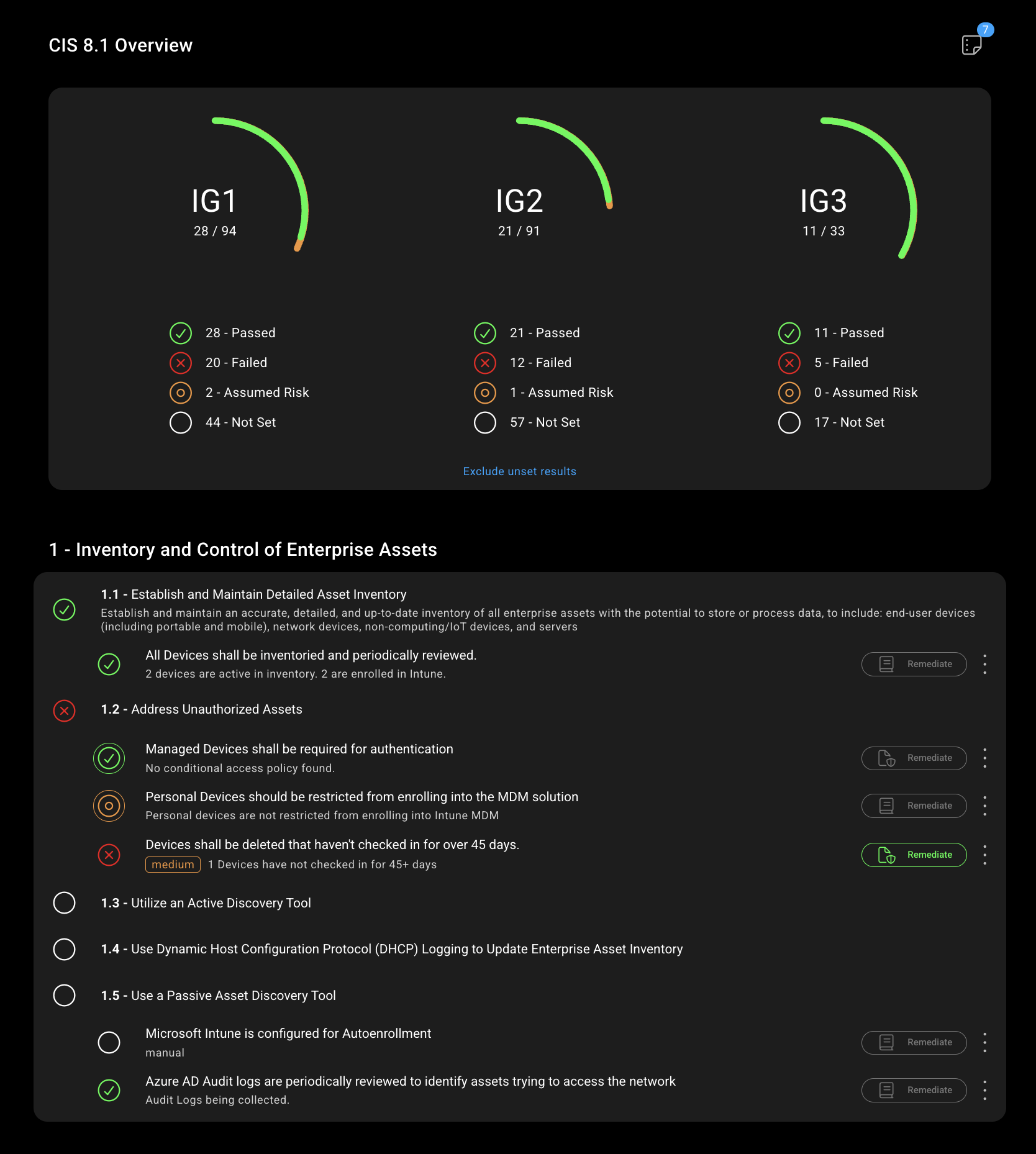
This assessment securely connects to Microsoft 365 using Microsoft's native access model to evaluate security configuration and posture, not user data. It compares your tenant against recognized security standards such as the CIS controls, NIST Cybersecurity Framework, and Microsoft security baselines.
The result is a clear, executive ready report that highlights misconfigurations, prioritize risks, and outlines recommended actions so leadership and IT teams can confidently decide what to fix first and why.
Have Question? Check out our FAQ
About Sourcepass MCOE
Sourcepass Center of Excellence for Microsoft (MCOE) is a Microsoft Solutions Partner for Security, recognized for delivering security outcomes across the Microsoft Cloud.
We apply Microsoft-aligned best practices and deep, real-world experience to help organizations reduce risk and strengthen security across Microsoft 365 with confidence.
.png?width=200&height=105&name=MS%20Solution%20Partner%20Security%20(1).png)
Microsoft 365 Security Assessment FAQs
-
What access is required?
Minimum required permissions, confirmed during kickoff, following least privilege principles.
-
What is a Microsoft 365 Security Assessment?
A read-only security review of your Microsoft 365 tenant that identifies configuration gaps, highlights risk areas, and provides a roadmap to improve security without changing anything.
-
Does the assessment make changes to our tenant?
No. It uses read-only access and does not enforce policies, change settings, or impact users. You will authorize access through a Microsoft OAuth URL.
-
How does the assessment access our environment and is it secure?
It connects using Microsoft's secure authentication model with limited, read-only permissions. No agents are installed. No credential are stored. No data leaves Microsoft 365.
-
What information does it review?
Microsoft 365 security configuration including identity, access controls, email, and collaboration security settings. It does not read email content, files or user data.
-
What standards are used?
Results are mapped to:
- CIS Controls
- NIST Cybersecurity Framework
- Microsoft security baselines
-
Is this a penetration test or compliance audit?
No. This is a security posture assessment focused on configuration and practical risk reduction.
-
Will this disrupt users or productivity?
No. The assessment is automated and read-only.
-
What happens after the assessment?
We review the results with you in an executive summary meeting and walk through findings and recommend next steps. You decide how and if you act.
%20(2).png?width=300&height=65&name=VERSION%201_MCOE%20Branding%20Mockups%20(6)%20(2).png)